In today’s digital economy, enterprises and crypto projects process vast volumes of transactions involving capital, contracts, and sensitive data. Financial institutions, supply-chain operators, healthcare organizations, and governments all face growing pressure to demand data protection and protect assets from cyberattacks, online threat actors, and emerging AI-driven threats.
Blockchain is often described as inherently secure. And from a technical standpoint, that claim is largely true. Yet despite its promise, many organizations still hesitate to rely on blockchain for mission-critical workflows.
The problem isn’t that blockchain is unsafe.
The problem is that most organizations cannot interpret what’s happening on-chain.
Raw blockchain data is open, but unreadable. This creates a trust gap that increases risk, complicates audits compliance, and slows enterprise adoption. Security without comprehension is not security at all.
What Makes Blockchain Secure by Design
Blockchain security is built on several foundational mechanisms that differ sharply from traditional centralized systems.
Cryptography and Key Encryption
Blockchain relies on strong cryptography to protect transactions:
- Key encryption ensures only authorized entities can initiate transactions
- Public-private key pairs replace password-based access
- Digital signatures verify integrity and authenticity
For enterprises, this mirrors established PKI security solutions and PKI credential management already used in secure communications. When paired with integrated hardware security modules, blockchain can meet demanding enterprise security requirements.
Consensus Mechanisms and Network Integrity
Instead of trusting a single authority, blockchain uses a consensus mechanism to validate activity across the network:
- Proof of Work (PoW)
- Proof of Stake (PoS)
- Delegated, consortium, and hybrid blockchain models
These systems defend against manipulation, including the well-known 51% attack, which becomes increasingly impractical on large networks and private blockchain networks used in enterprise and consortium settings.
Immutability and Auditability
Once recorded, blockchain transactions are extremely difficult to change:
- Records are tamper-resistant
- Changes require broad network agreement
- Every transaction creates a permanent audit trail
For organizations managing regulatory reporting, financial reconciliation, or security data sovereignty, immutability is a major advantage.
The Enterprise Reality: Where Risk Still Exists
If blockchain is secure, why do enterprises still experience security issues?
The answer lies in visibility.
The Transparency Paradox
Blockchain is technically transparent, but operationally opaque.
Enterprises struggle with:
- Overwhelming transaction volumes
- Complex smart-contract interactions
- Pseudonymous wallets with no human-readable context
- Manual reviews that take hours per transaction
This is why many organizations still rely on spreadsheets, parallel databases, or expert auditors to interpret blockchain activity. The system is secure, but unreadable.
As explored in Clear Visuals: Easily See Blockchain Activity at a Glance, transparency alone doesn’t create trust—clarity does.
https://hindsight.vip/blog/clear-visuals-easily-see-blockchain-activity-at-a-glance
Why Visualization Is Now a Vital Security Solution
Modern enterprise security depends on rapid understanding, not just encryption.
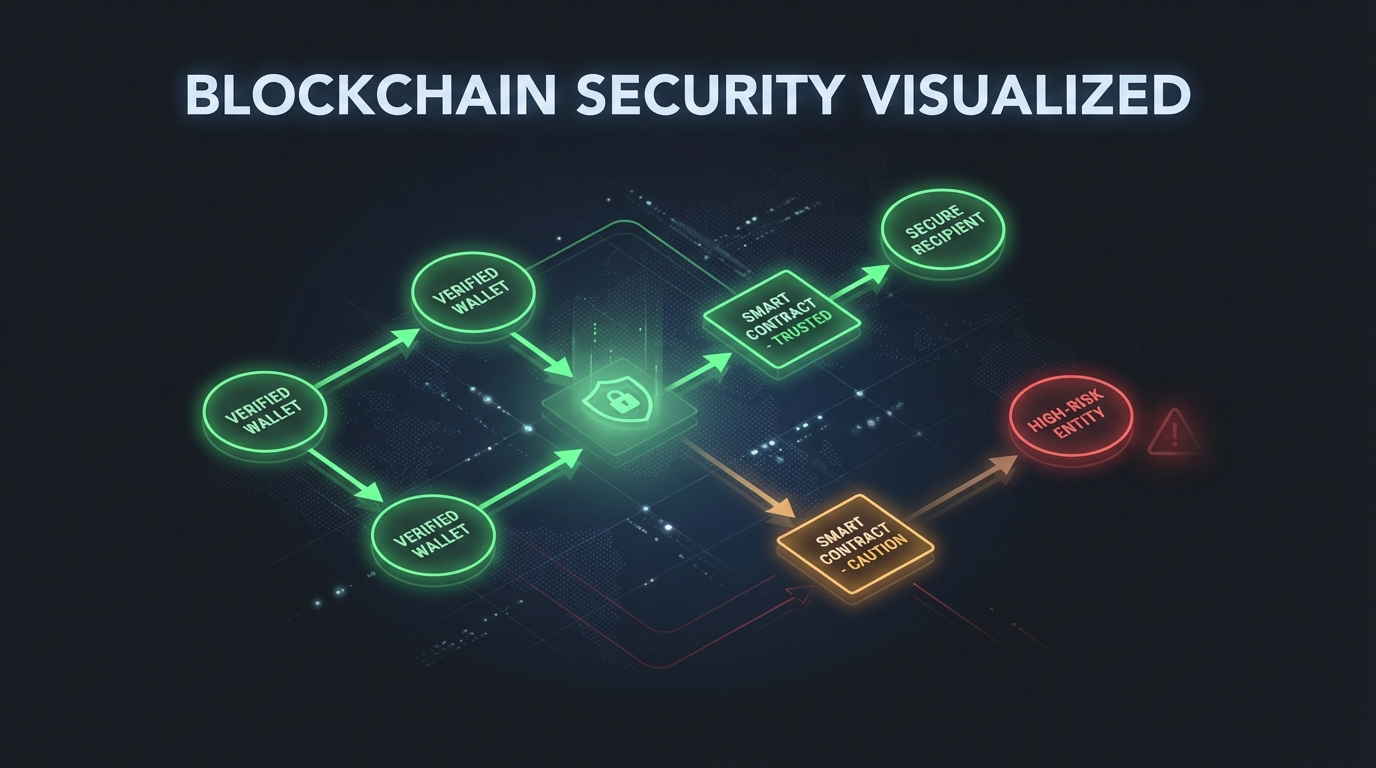
Blockchain visualization turns raw data into readable intelligence:
- Colors indicate trust levels and risk
- Shapes represent wallets, contracts, and exchanges
- Flows show how assets move across systems
Instead of reviewing logs, teams can see behavior.
This visual layer dramatically improves:
- Fraud detection
- Incident response
- Compliance workflows
- Executive decision-making
How Visual Explorer and Shape Mode™ Close the Trust Gap
Hindsight VIP’s approach focuses on accessibility without sacrificing rigor.
Visual Explorer for Enterprise Monitoring
Visual Explorer translates blockchain activity into structured, visual maps designed for non-technical professionals. It allows organizations to:
- Track transactions across chains
- Identify suspicious wallet behavior
- Verify smart-contract interactions
- Support a risk management procedure and audits
- Strengthen governance through advisory extended security practices
This approach aligns with zero-trust models, where nothing is trusted until verified—visually.
The broader strategy behind this is explained in
Unlocking Blockchain Insights: Multi-Chain Visualization for Network Performance
https://hindsight.vip/blog/unlocking-blockchain-insights-multi-chain-visualization-for-network-performance
Shape Mode™: A Visual Grammar for Blockchain
Shape Mode™ creates a consistent visual language:
- Circles = wallets
- Squares = smart contracts
- Triangles = exchanges
Combined with color-based risk indicators, this system standardizes how teams interpret blockchain activity—reducing misinterpretation and speeding response times across the organization.
The origin of this visual-first philosophy is detailed in
From Frustration to Clarity: The Story Behind Hindsight VIP’s Visual Blockchain Tools
https://hindsight.vip/blog/from-frustration-to-clarity-the-story-behind-hindsightvips-visual-blockchain-tools
These enterprise-grade examples show how the same visual security layer can support each use case across teams and industries.
Financial Services Industry
- Faster AML and KYT reviews
- Reduced manual analysis
- Stronger defenses against blockchain attacks
Supply Chain and Manufacturing
- Immutable provenance tracking
- Visual custody chains for regulators
- Runtime protection against tampering
Healthcare and Data Governance
- Protection of sensitive data
- Clear access management controls
- Strong compliance with data-sovereignty requirements
Risk and Security Teams
- Visual api discovery
- Monitoring the changing api security landscape
- Early detection of abnormal transaction flows
These use cases demonstrate why visualization has become one of the most vital security solutions for enterprise blockchain adoption—and a practical way to keep blockchain blockchain safe in day-to-day operations.
Addressing Emerging Threats
Blockchain security continues to evolve alongside new risks:
- Sophisticated AI-driven threats
- Cross-chain exploits
- Long-term concerns such as post-quantum breach scenarios
Visualization does not replace cryptography. It strengthens the security system by enabling earlier detection, faster human understanding, and better governance when paired with cybersecurity best practices and tested frameworks.
Why Blockchain Is Secure — When Enterprises Can See It
Blockchain is already one of the most secure transaction systems ever created. But security that cannot be understood cannot be trusted.
For enterprises, the future of blockchain adoption depends on visibility:
- Seeing risk before it escalates
- Verifying transactions without decoding raw data
- Empowering teams beyond engineers
Visualization bridges the final gap between blockchain being technically safe and operationally secure.
Blockchain is secure—but only if your organization can read it.
Hindsight VIP provides enterprise-grade visual trust infrastructure that turns complex blockchain data into clear, actionable intelligence.
👉 Learn more about enterprise deployment, compliance use cases, and visual security architecture:
https://hindsight.vip/enterprise
If you’re evaluating blockchain for a production environment, ask for a free risk assessment and request the platform white paper to see how the approach supports enterprise requirements end to end.
Blockchain security isn’t just about encryption—it’s about clarity. Hindsight VIP helps enterprises see risk, verify transactions, and protect sensitive data through visual blockchain intelligence.